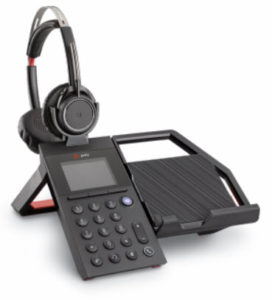
 I finally had a chance to put the Plantronics Voyager 8200 UC headset through some paces. This $380 (MSRP) headset sports boomless dual microphones – one on the front edge of each ear cup. Of course, this is a departure from “normal” UC headsets, and takes getting used to. But that’s not the only thing different. Dual mode active noise canceling (ANC) makes for a much quieter environment – whether you’re in a busy room, or mowing the grass (more on that later). This headset can be connected to two sources at one time, such as a PC and a mobile device. For a PC connection, the included BT600 USB Bluetooth dongle comes into play, and provides just under 100 feet of range. For a mobile device, it gets paired like any other Bluetooth device. There is also a removable 3.5mm audio cable included – perfect for watching those movies on the seat-back in front of you on a long flight.
I finally had a chance to put the Plantronics Voyager 8200 UC headset through some paces. This $380 (MSRP) headset sports boomless dual microphones – one on the front edge of each ear cup. Of course, this is a departure from “normal” UC headsets, and takes getting used to. But that’s not the only thing different. Dual mode active noise canceling (ANC) makes for a much quieter environment – whether you’re in a busy room, or mowing the grass (more on that later). This headset can be connected to two sources at one time, such as a PC and a mobile device. For a PC connection, the included BT600 USB Bluetooth dongle comes into play, and provides just under 100 feet of range. For a mobile device, it gets paired like any other Bluetooth device. There is also a removable 3.5mm audio cable included – perfect for watching those movies on the seat-back in front of you on a long flight.
This headset sports 24 hours of battery life for listening, but that drops to roughly 20 hours of talk time. When in standby mode, this headset should hold a charge for quite a while. Plantronics says a month, but I haven’t tried it that long. I use it too often! But more importantly, how does it sound? 40mm drivers give damn good sound, whether it’s speech related as part of a UC conversation, or you’re head-banging to Motley Crue.
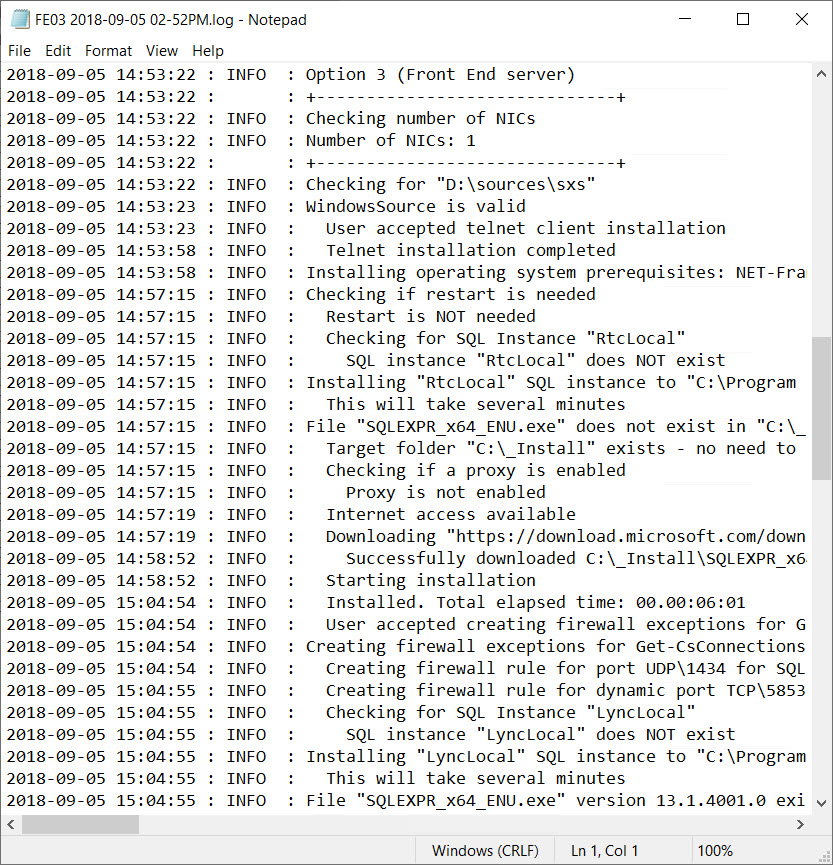
Configuration/Setup
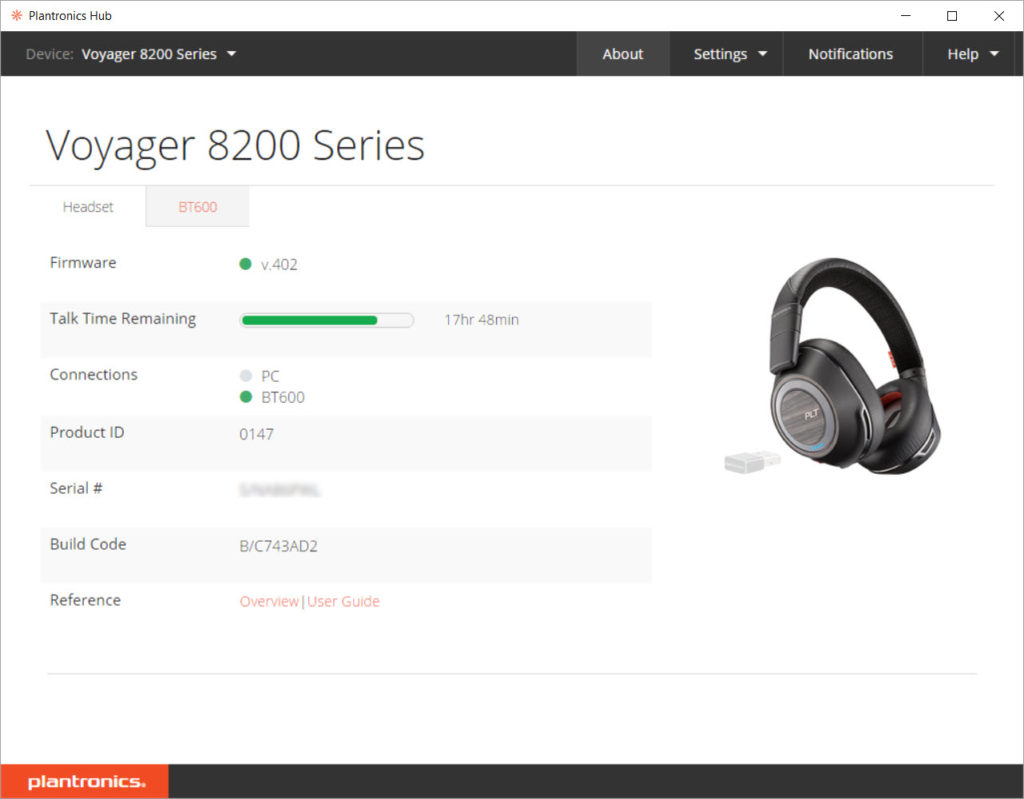
The free download Plantronics Hub software allows for configuration of the headset, as well as upgrading the firmware. That second part is key here.
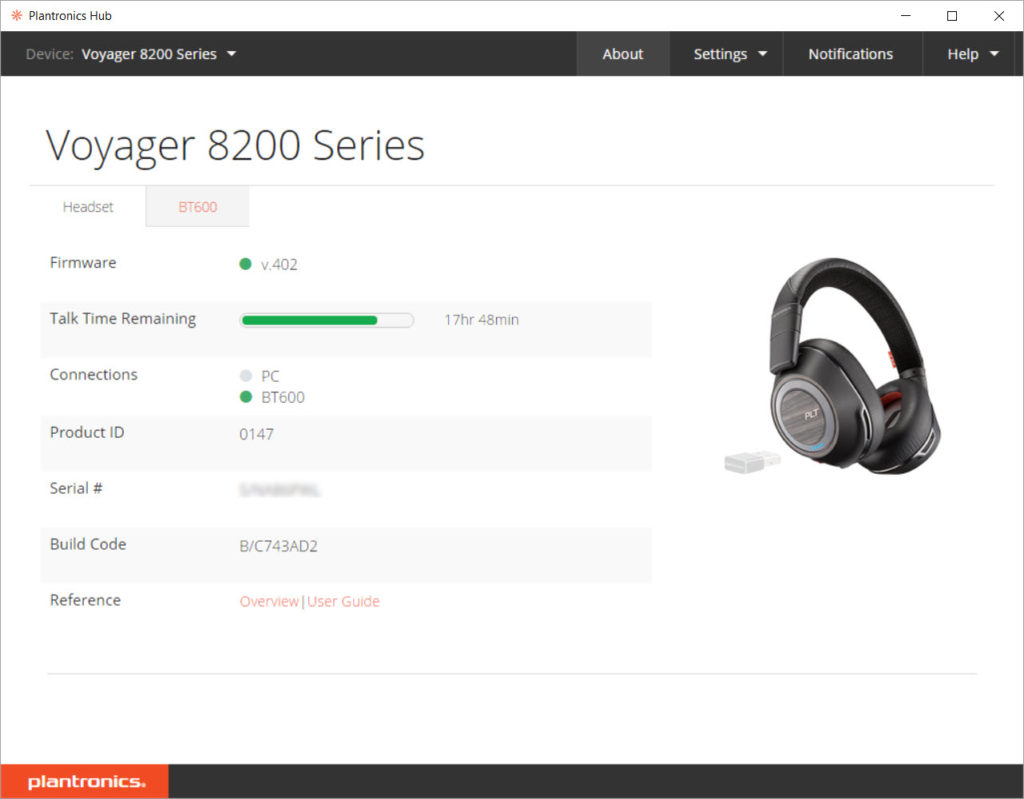
When I first got the headset, receiving audio during calls had a horrible clipping problem. Within 2 minutes, I’d opt for a different endpoint as it was very distracting. Music from my mobile device sounded fine, however. I tried various options in the software, such as disabling HD audio, etc. But that didn’t work. Upgrading the device to the latest firmware resolved the problem, and the audio has been quite clear ever since. The firmware upgrade process is pretty straightforward. Once the headset is powered on, it appears as the ‘headset’ tab in the Hub software. Click on the ‘Notifications’ button in the upper right, then ‘Check for Updates’. The upgrade process only takes a couple of minutes over the air. Other things in the Plantronics Hub software include the following screens under ‘Settings’:
General
Answering Call Alert – This provides verbal feedback when you answer a call from the headset. You’ll hear ‘Answering Call’.
Audio Channel Tone – Hear a tone that the headset is on and ready.
Caller ID – With this enabled, you hear verbal prompt of incoming caller ID info from you cell phone’s contacts list.
Mute On/Off Alerts – Hear feedback when muting and unmuting the headset. Options include various tones or a verbal alert.
Mute Reminder – Get a reminder that you’re muted. Some nice options here include feedback when you start talking, but you’re muted. This is similar to the on-screen feedback in Teams for the same thing.
Online Indicator – This is an on-headset LED indicator to alert others around you that you’re in a call.
Second Incoming Call – This setting configures how you’re alerted when you’re on one system, such as a Skype for Business call, and a mobile call comes in.
Software Settings related to feedback and logging.
Ringtones & Volume
Ringtone – Whether you hear a ringtone from the device.
Sidetone – This is how much (if any) of your own voice you hear while on a call. Most people take this for granted and don’t realize you hear your own voice when talking – until it’s not there. This option has Low/Medium/High settings. I find that I needed it to be on high. Feedback from me on this is it would be nicer if this was more granular, and if the high setting was a litter louder.
Volume Level Tones – This setting provides feedback when you’re adjusting the volume on the headset. Options include feedback at every level, or just minimum and maximum.
Softphones & Media Players
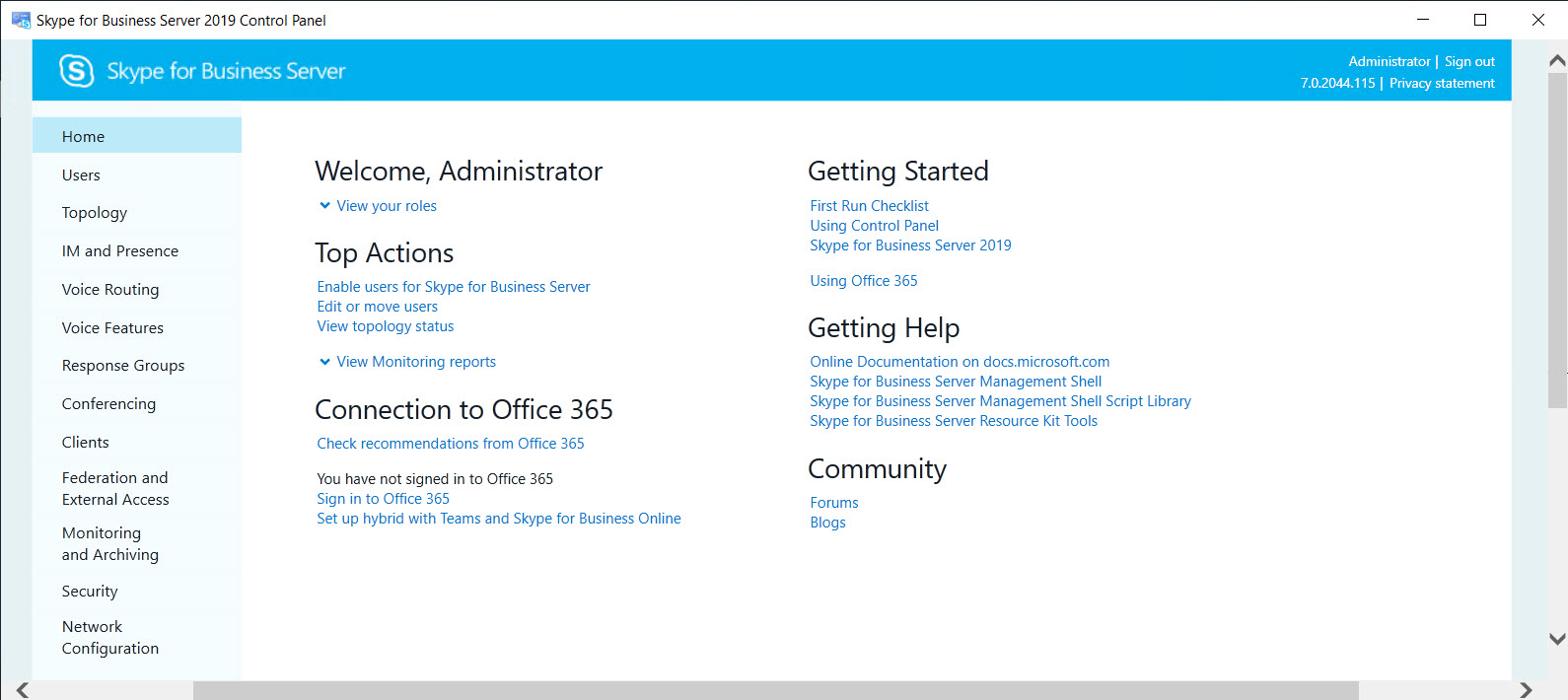
Target Softphone – This sets what the headset defaults to. Many are listed here, including Avaya, Cisco, Skype for Business, Broadsoft, consumer Skype, etc. An option I don’t see here is for Microsoft Teams.
Media Player Action on Incoming Call – Here is a nice feature that dictates what happens to your media player when there is an incoming call. ‘Pause & Resume’ is nice.
Softphones & Media Players – This is an extensive list of various UC clients and media players that you can enable/disable access to.
Sensors & Presence
Wearing Sensor – Mostly a master setting for everything else.
Active Call Audio – This is a nice option that defines what action is taken when take off the headset while you’re in a call. ‘Mute microphone’ is my choice, but you can also transfer the call to your mobile device or take no action.
Auto-Answer – Another nice option to reduce fumbling. This dictates what happens when you put the headset on when your phone rings. Having it answer the call is nice, avoiding having to click a button on screen or press one of the buttons on the ear cups.
Auto-Pause Music – This option is specific to streaming music, and whether you want to end/resume the stream when you remove the headset or put it back on.
Aware for Microsoft – This is nice idea, but I couldn’t get it to work. Supposedly, when enabled, this will update your Skype for Business status when you’re in a mobile call.
Wireless
Extended Range Mode – if you’re finding that you’re often near the edge of the reception coverage, you can enable this setting to provide a little more range. The downside is that it disabled wideband audio.
HD Voice – This provides for richer audio, but consumes more battery power. But hey, that’s why they’re rechargeable, right?
Streaming Audio – This enables streaming audio mobile device, but at the cost of battery life. But we simply MUST have our Van Halen, right?
Advanced
Anti-Startle – Helps reduce loud noises for your hearing protection.
Noise Exposure – This is a tad different from the Anti-Startle. This monitors overall sound to make sure you’re below the level set by the EU government. Anti-Startle is more for sudden noises, while this is overall throughout the day.
For those in the enterprise, Plantronics Manager Pro can be used to maintain and monitor devices via a web browser.
Review
A great feature of this headset is its Active Noise Cancellation: The headset works great regardless if the active noise cancellation (ANC) is turned on. When enabled, it does a great job of reduction of steady noise sources such as airplane or lawn mower engine noise. Even if you aren’t listening to an audio source, the reduction in noise means you could take a quiet nap on a flight. When the ANC is turned off, you don’t hear a big change in the quality from audio sources like you do with some Bose headsets.
Controls on the right ear cup include a on/off hook button on the side, power and mute switches on the back. A USB micro port on the bottom of the right ear cup allows for charging, and a 3.5 mm jack next to that is for the included audio cable. Also on the right ear cup are several LEDs. A series of blue LEDs cycle when the headset is charging. A single blue LED lights up when you’re in a call, and it changes to red if you’re muted. On the left ear cup, there is the ANC switch on the back, play/pause, next & previous buttons on the side surrounded by the volume dial. The volume dial turns about 15 degrees in either direction to raise or lower the volume. Personally, I’d prefer that this be a continuous dial. On the front of each ear cups are the microphones used for both speech and noise cancellation.
Turning on the headset yields several voice notifications, including that it’s powered on, the battery level, and what it’s connected to. Pressing the power switch up and releasing will repeat these notifications. The option to mute the headset when taking it off is great, as is the ability to answer the phone automatically when putting it on. I really like these as they streamline the whole experience.
The Dynamic Mute Alert feature is advertised as “Dynamic mute alert senses and alerts you when you talk when muted.” This didn’t always work as I expected. Sometimes it would take up to 10 seconds before I would hear the “muted” notification. I would expect it to be a little faster. Sometimes, I wouldn’t hear it at all. That’s too bad, as this would be a great feature.
Other than audio quality, there are some things I always look at when testing a headset for use in the office.
Fitment: Fit of the headset is very good. It doesn’t squeeze my giant melon like the original Jabra Evolve 80 headset does. The 8200 UC is comfortable enough to wear on hour+ long conference calls. But lets look at a couple of other tests.
Sweat test: Over the ear headsets can generally get warm since they completely encase your ears. These are no different, even in a comfortable office environment. Mowing the grass with the 8200 UC headset results in pretty sweaty ears, but no degradation in audio quality or fit. And that includes not getting overly slippery.
Head tilt test: This is the test where you look down towards the floor, chin touching your chest, and see if the headset slides off your head. Over the ear headsets generally do well because your ears tend to keep it in place. With this headset, it pretty much stays in place unless you nod strongly, and then you can feel the headband slide forward a bit, but not enough to pull the headset off. I’ve had some where they slide right off my head when looking down.
Overall audio test: I used this headset in many Skype for Business and Teams calls – both one-on-one and conferences. Once the firmware issue was resolved, the headset worked great each time. I had no problems with clarity for received audio, and other call participants said my sending audio was also quite clear. For Bluetooth audio, again, the headset worked great when paired to my cell phone. I had two instances where the connection to the cell phone dropped, but I was unable to determine whether the cause was on the mobile or headset side. In both instances, it immediately reconnected. One issue I did run into is that the Bluetooth audio would cut out for a few seconds when I would reach the edge of the PC dongle’s range. This didn’t happen every time. Usually I would just hear the voice notifications “PC connected” or “PC disconnected”. But it would happen occasionally. When using the included 3.5mm audio cable for connecting to other devices, I had not problems at all. I watched several movies when traveling internationally. The ANC worked as expected, whether on a flight or cutting the grass. It even silenced the sound of air coming through the AC vent in my office, and that’s a sound I don’t generally notice.
Overall
Pros: Great sound quality, once the firmware was updated; Connecting to multiple audio sources; Great fit; Nice features in configuration software; Voice notifications; Plenty of hardware controls; Excellent battery life; Quite comfortable; Excellent build quality.
Cons: Volume control should be continuous dial; When at the edge of the PC coverage range, sporadically causes short loss of audio from mobile; headset comes with simple pouch instead of hard case; Dynamic Mute Alert feature is very inconsistent; Sidetone adjustment could be more granular, and have a wider ange.
Overall: The Plantronics 8200 UC is a great sounding headset that works great in Skype for Business and Teams, as well as with a mobile device, while blocking out distracting noise. I’d love to see improvements in the Dynamic Mute Alert feature as I’m somewhat jaded by the same on-screen feature in Microsoft Teams. I recommend this headset for those who like over-the-ear headsets with active noise cancellation. I plan on continuing to use this headset.
Ethics Statement: Companies may send software, hardware, or other products or samples to me in order for me to review such samples and determine whether I will provide a review of the product on UCUnleashed.com. I do not accept any samples on any preconditions, such as, that I will agree to provide a review simply because the company sent me a sample, or that I will only provide a positive review. Please note that companies may provide these samples before the product is commercially available, in which case, I may agree to an embargo with the company or its PR firm. This means I agree not to publish the review or associated news until a given time.










Follow Me