Removing PIC Federation Configuration for AOL and Yahoo!
In November of 2012, Microsoft announced that Public IM Connectivity (“PIC”) federation for AOL and Yahoo! would be ending. Microsoft gave a good advanced warning, eventually saying it would cease on June 30, 2014. They held true to that date, and connectivity via the traditional methods is no longer available. Some have even reported that Yahoo! federation stopped working as early as April 2014.
I’ve run some reporting using Get-CsFederatedConversationDetails.ps1 and verified that other than my occasional conversations with dear old Mom, no one was using these PIC providers. So no big loss, and certainly, no business impact. But, for those orgs that DO require connectivity to AOL, such as some of the hedge fund groups, AOL does have a service that will allow your users to communicate with AOL users. It does. however, require a monthly per user fee. More information can be found at https://aimenterprise.aol.com/microsoft/.
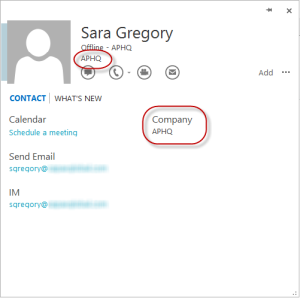
For now, any AOL or Yahoo! contacts that users have in their contacts list will show as Presence Unknown.
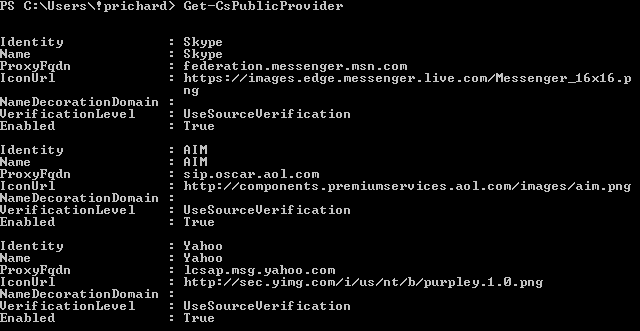
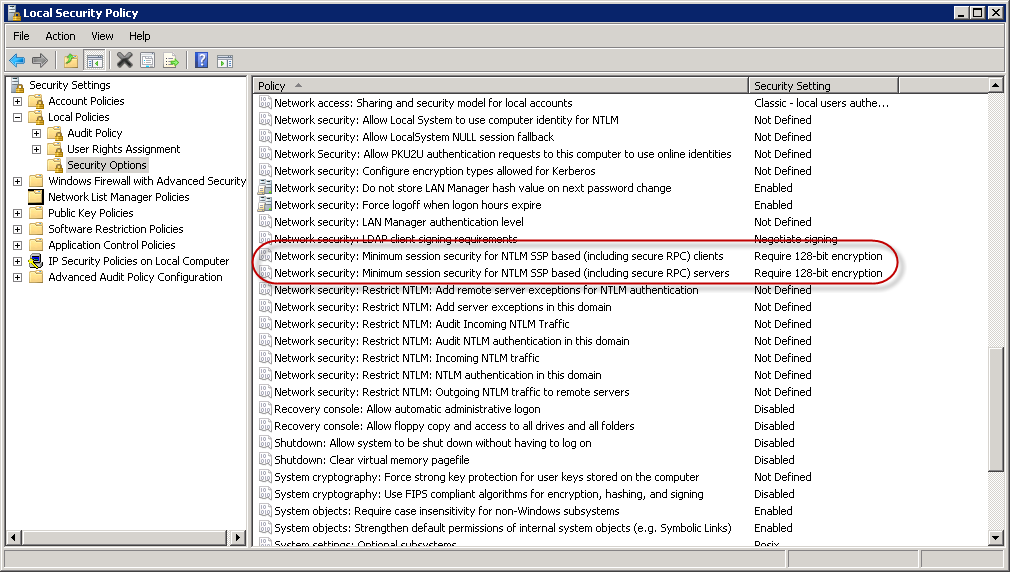
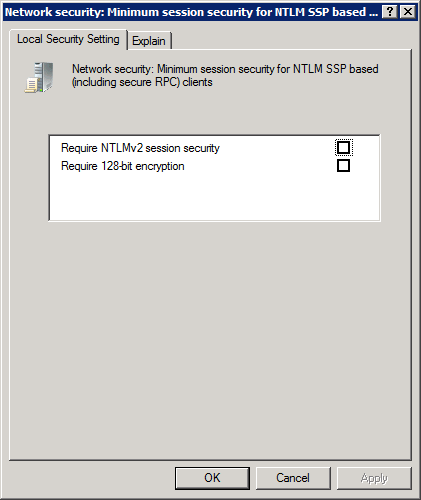
It now makes sense to remove the related configuration for your Lync config – if you had it configured previously. PIC federation is configured via Public Providers. We can see the public providers configured via the Get-CsPublicProvider cmdlet, as shown below.
Removing the configuration for AOL and Yahoo! can be performed with one line of code.
Get-CsPublicProvider | Where-Object {$_.ProxyFQDN -eq "sip.oscar.aol.com" -or $_.ProxyFQDN -eq "lcsap.msg.yahoo.com"} | Remove-CsPublicProvider
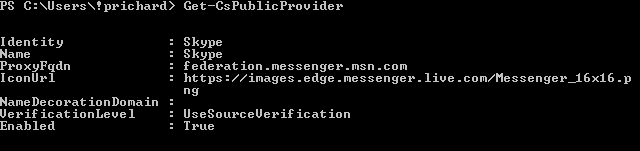
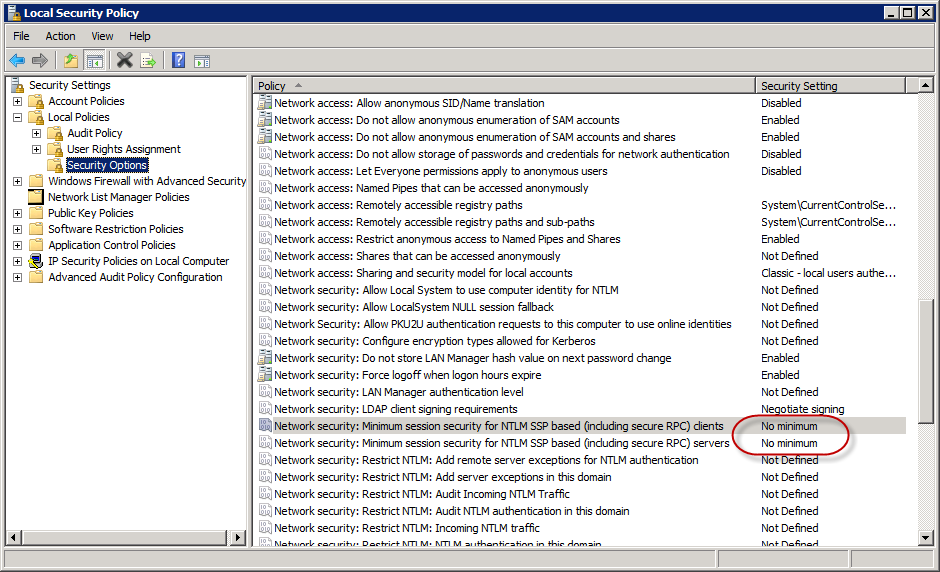
This will remove just the AOL and Yahoo! public providers, and leave any others, like Skype, as shown below when running Get-CsPublicProvider again.
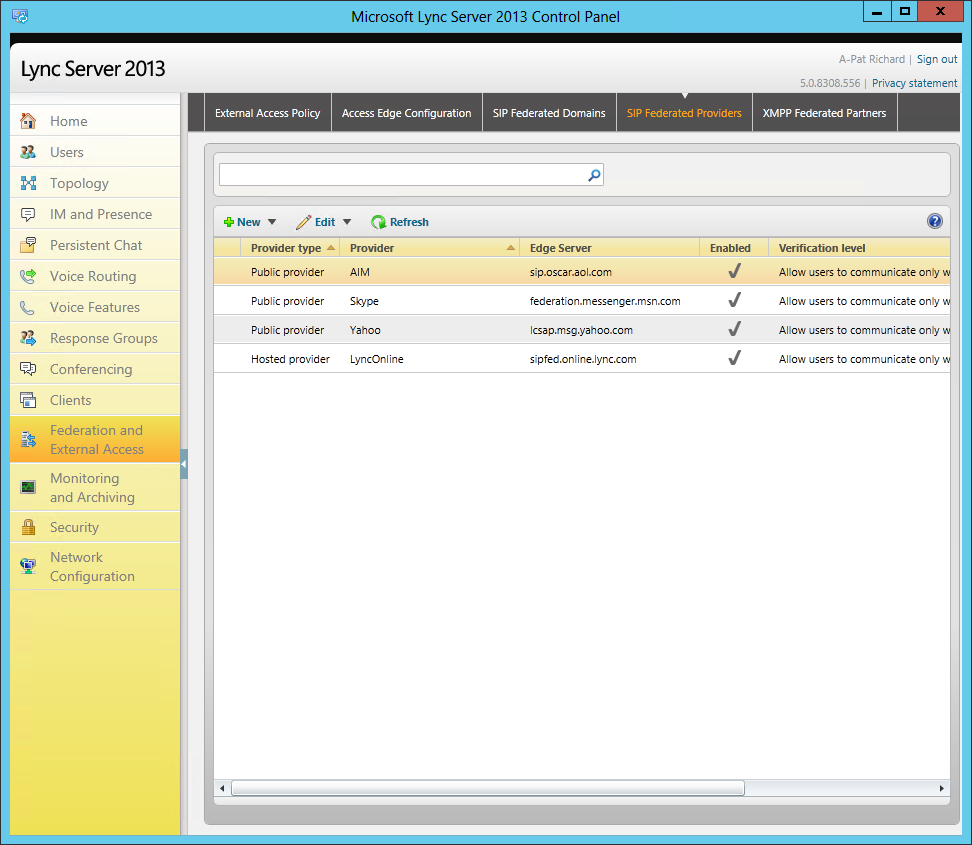
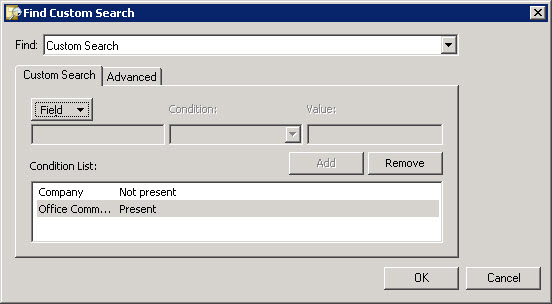
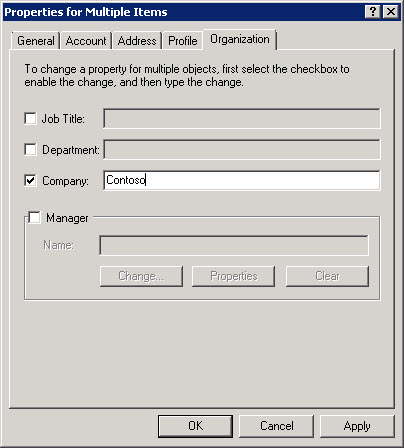
If you’re a little apprehensive about using PowerShell (and you shouldn’t be – embrace the shell!), we can also remove the public providers in the Lync Server Control Panel. Navigate to Federation and External Access>SIP Federated Providers. You’ll see a list of both public and hosted providers as shown below.
Merely select the appropriate provider you’d like to remove, select Edit>Delete. Once you’ve removed both the AOL and Yahoo! providers, you’re left with any remaining public and hosted providers as shown below.
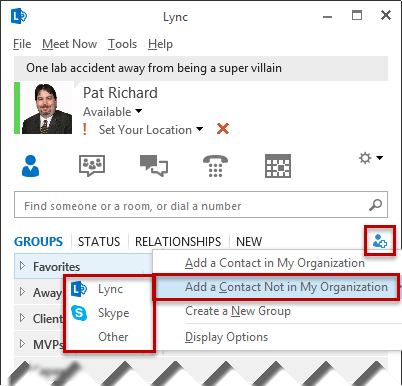
Once clients refresh their config, the options for AOL and Yahoo! will no longer be available when adding new contacts.
Users wills still need to manually remove AOL and Yahoo! federated contacts from their contacts list, though.








Follow Me